API security best practices: Protecting software and data from cyber threats
APIs connect software with a diverse range of services, making development easier and cheaper. Yet as organizations invest in API development, new risks arise. Without API security best practices, businesses face a growing landscape of cyber threats and vulnerabilities. Protecting API integrations is crucial for safe digital growth.
In this article, we will walk you through the essentials of cybersecurity for APIs. You will learn how to secure your APIs at every stage, and discover the most effective strategies to shield your data and operations. Whether you are launching new products or modernizing existing ones, these insights will help you build reliable, secure integrations.
Understanding the API threat landscape
APIs are powering apps, connecting partners, and driving new business models. But as every new feature brings more integrations, it also creates new doorways for attackers. Today, businesses face a complex array of data protection cyber threats that target not just user interfaces, but also everything that happens behind the scenes.
Most common API threats
Shadow APIs
Many risks stem from the huge scale of API development in modern organizations. As companies move faster, APIs multiply and become harder to track, leading to “API sprawl”. This makes it easy to miss undocumented or outdated endpoints, also known as shadow or zombie APIs. Without effective cybersecurity for APIs, these forgotten integrations increase the attack surface and provide opportunities for cybercriminals.
Broken authorization
Broken authorization is one of the most dangerous vulnerabilities, allowing attackers to access data or admin features not meant for them. The OWASP API security top 10 ranks this type of issue as a top risk year after year.
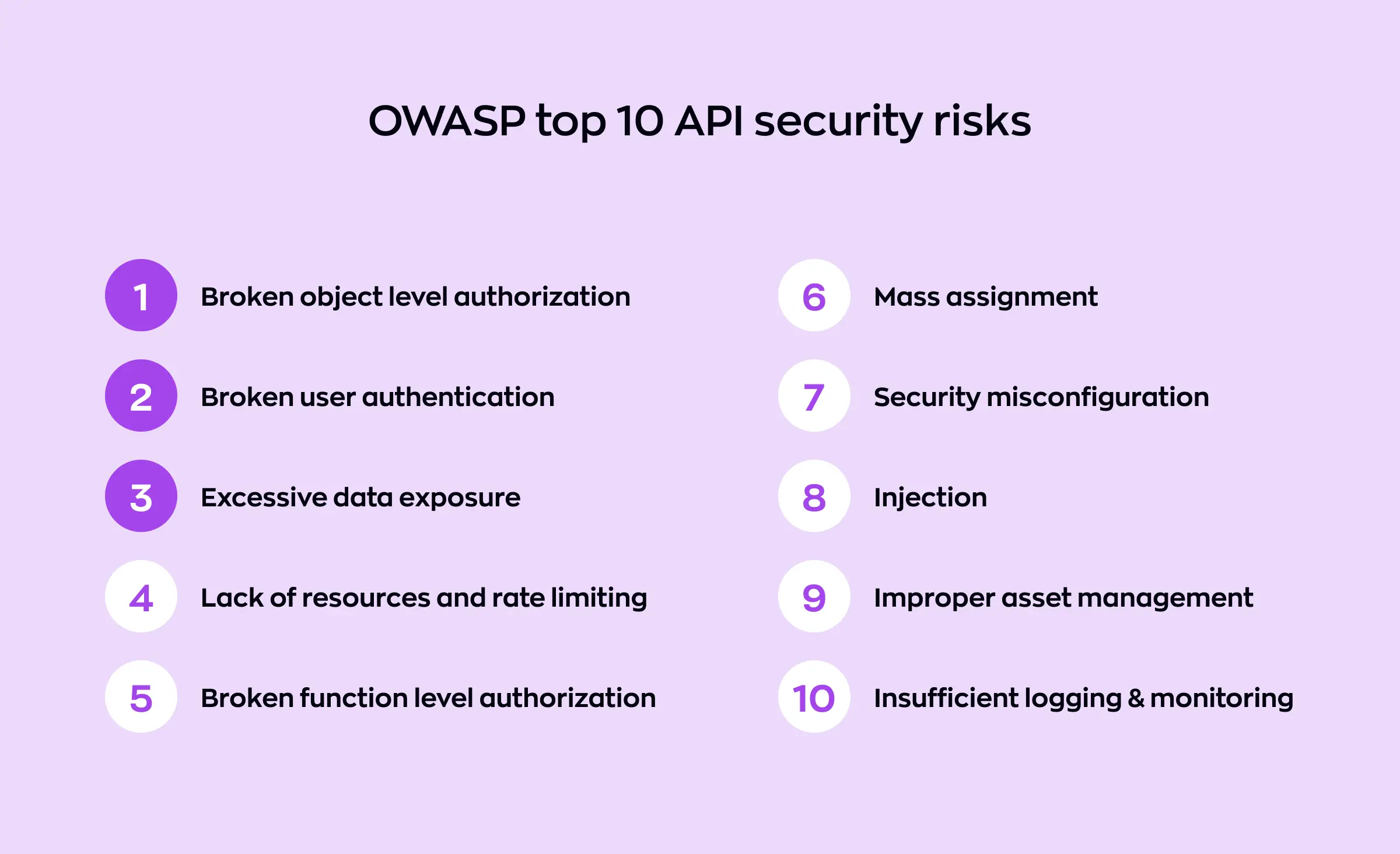
Attackers are quick to find APIs that don't properly check IDs, permissions, or user roles and exploit them to steal information. Recent incidents show how these flaws can damage both revenue and reputation.
Authentication weaknesses are another frequent source of trouble. Mistakes in token handling, poor session management, or buggy implementation give attackers a chance to impersonate real users. High-profile breaches have shown what can happen when API vulnerability management isn't a continuous focus.
Excessive resource usage
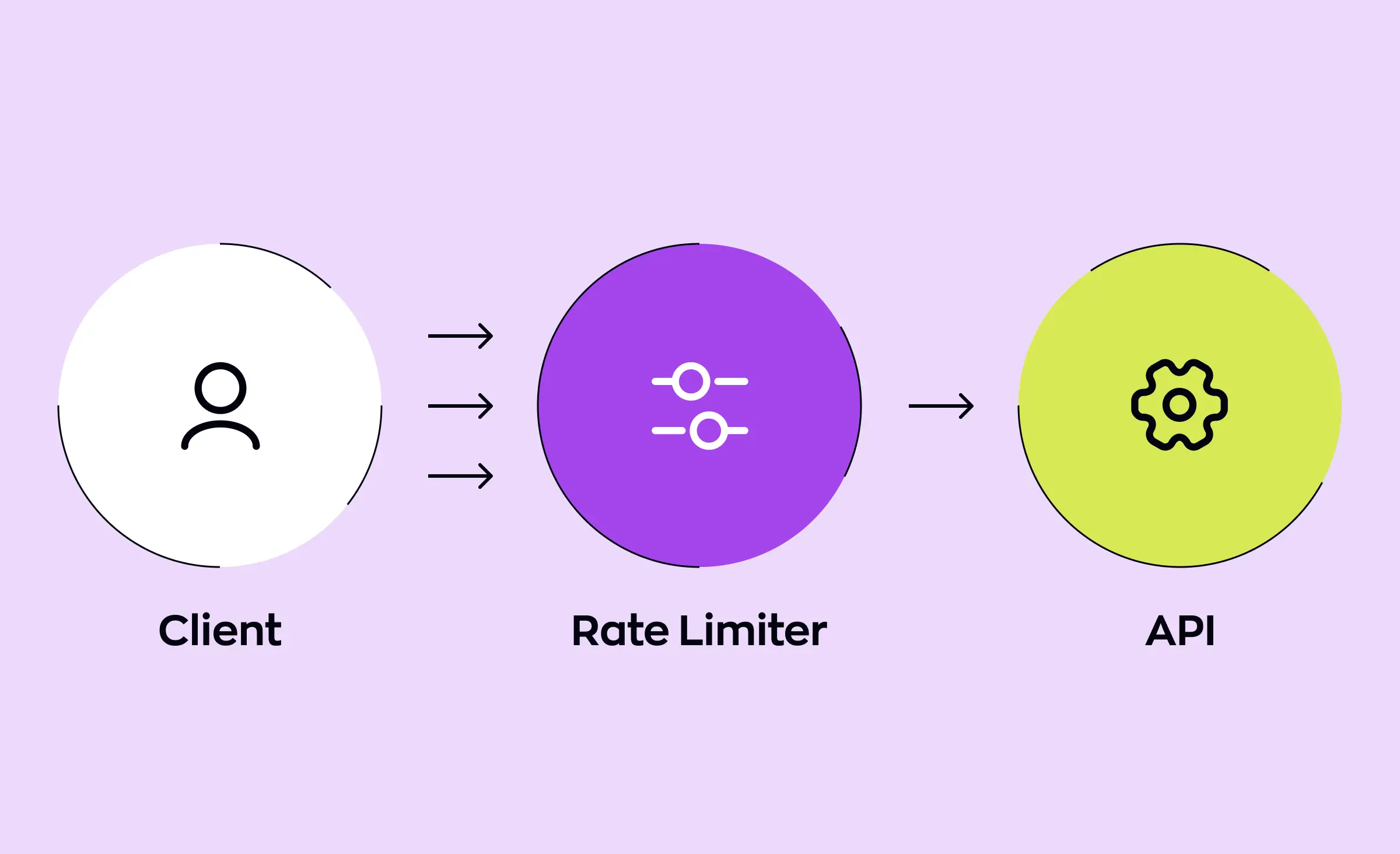
Not all cyber attacks try to steal data — some aim to shut down services. Many APIs lack rate limits or quotas, making them targets for DDoS or “resource exhaustion” attacks. Automated bots can send floods of requests, forcing business-critical services offline and causing direct financial losses. For companies that rely on secure integrations, unchecked APIs mean real business risk.
Microservices and APIs risks
Cloud security is now an essential part of application security. As teams build on cloud platforms and connect resources through APIs, any misconfigured endpoint could expose sensitive data. Distributed systems and microservices security also present new challenges. When dozens or hundreds of internal microservices talk via APIs, every connection must be protected — missing authentication or encryption can become a weak point for the whole system.
What businesses can do
Maintaining application security today means knowing exactly which APIs are active, what versions are running, and what each integration does. Without proper API threat detection and ongoing monitoring, organizations can't react quickly to new data protection cyber threats. Effective API gateway security supports both attack prevention and real-time visibility across all services.
Staying ahead means adopting API security best practices at every stage of the lifecycle. This involves:
- Enforcing input validation on all APIs for both first-party and third-party integrations.
- Keeping an up-to-date inventory and monitoring for shadow APIs.
- Focusing on secure integrations with strong authentication and authorization.
- Applying regular API vulnerability management and threat detection for every service.
Every company that values growth and reliability needs to make API development and security central to their plans for the future. With the right application security strategy and robust cloud security tools, you can turn APIs from a point of risk into a core business strength.
Authentication and authorization: Keys to API protection
Digital services depend on accurate user identification and access controls. When it comes to API authentication authorization, even a small error can have major consequences. A misplaced token or misconfigured permission can result in unauthorized users accessing sensitive data or critical business functions. That's why these security layers are often the main target for hackers trying to break into modern platforms.
Building digital identity and authentication
Ensuring every user and system can be recognized, verified, and trusted is the core of digital identity and authentication. This means every API request must come from someone or something allowed to use it — whether that's an employee, partner, client, or another application. Properly managing digital identities not only safeguards your assets but also builds user trust.
OAuth2, API keys, and more
Several proven methods set the foundation for API authentication authorization. OAuth2 API security is one widely adopted solution, enabling secure access without sharing passwords. OAuth2 lets users grant access to their data while keeping login details private. In comparison, API keys security provides quick access for trusted applications, but keys must be generated and managed with care to prevent leaks or unauthorized use.
When designing secure API systems, using the right method for each use case is vital. For instance, public services can use short-lived tokens, while internal systems might rely on mutual TLS or signed requests. Secure API design always considers the risk of stolen or misused credentials and puts protections in place before issues arise.
Security by design
Incorporating careful authentication and secure API design from the very start helps avoid expensive fixes down the road. For complete cybersecurity, choose tools and partners with a track record of robust API authentication authorization. Make sure every integration gets the same careful treatment. This approach is essential for protecting API integrations and keeping your business safe in a fast-moving digital landscape.
Protecting API integrations across industries
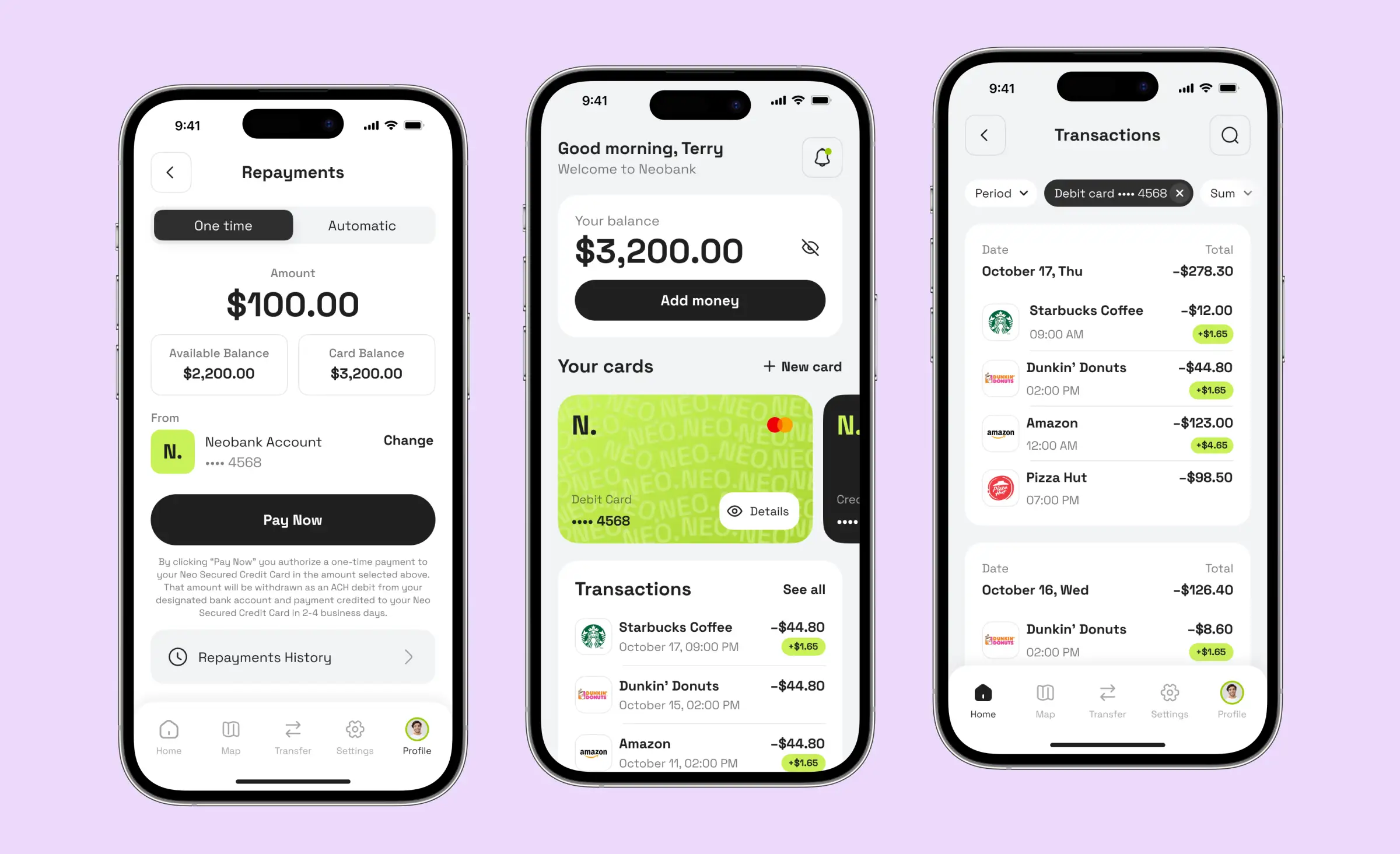
Every industry has unique needs for API authentication authorization. In fintech security, ensuring only verified accounts can move money helps avoid fraud and meet regulatory standards. Similarly, healthcare security requires robust controls to protect patient records and maintain compliance. Weak controls here can lead to damaging and expensive breaches.
API security best practices also recommend checking permissions at both user and object levels, meaning even authenticated people or applications are limited in what they can access. This reduces harm if an attacker slips through one layer of defense.
A modern online service might use OAuth2 tokens for customers, API keys for partners, and role-based access for internal staff — all managed by a centralized identity platform. This approach can simplify backend development while supporting data privacy and regulatory requirements.
Data protection strategies for APIs
Every day, APIs deal with valuable information — customer records, payment details, and even medical files. This makes APIs a prime target for data protection cyber threats. When attackers find weaknesses, the results can be costly breaches or loss of customer trust. Protecting API integrations should be a priority for any company that relies on digital connectivity.
Data encryption
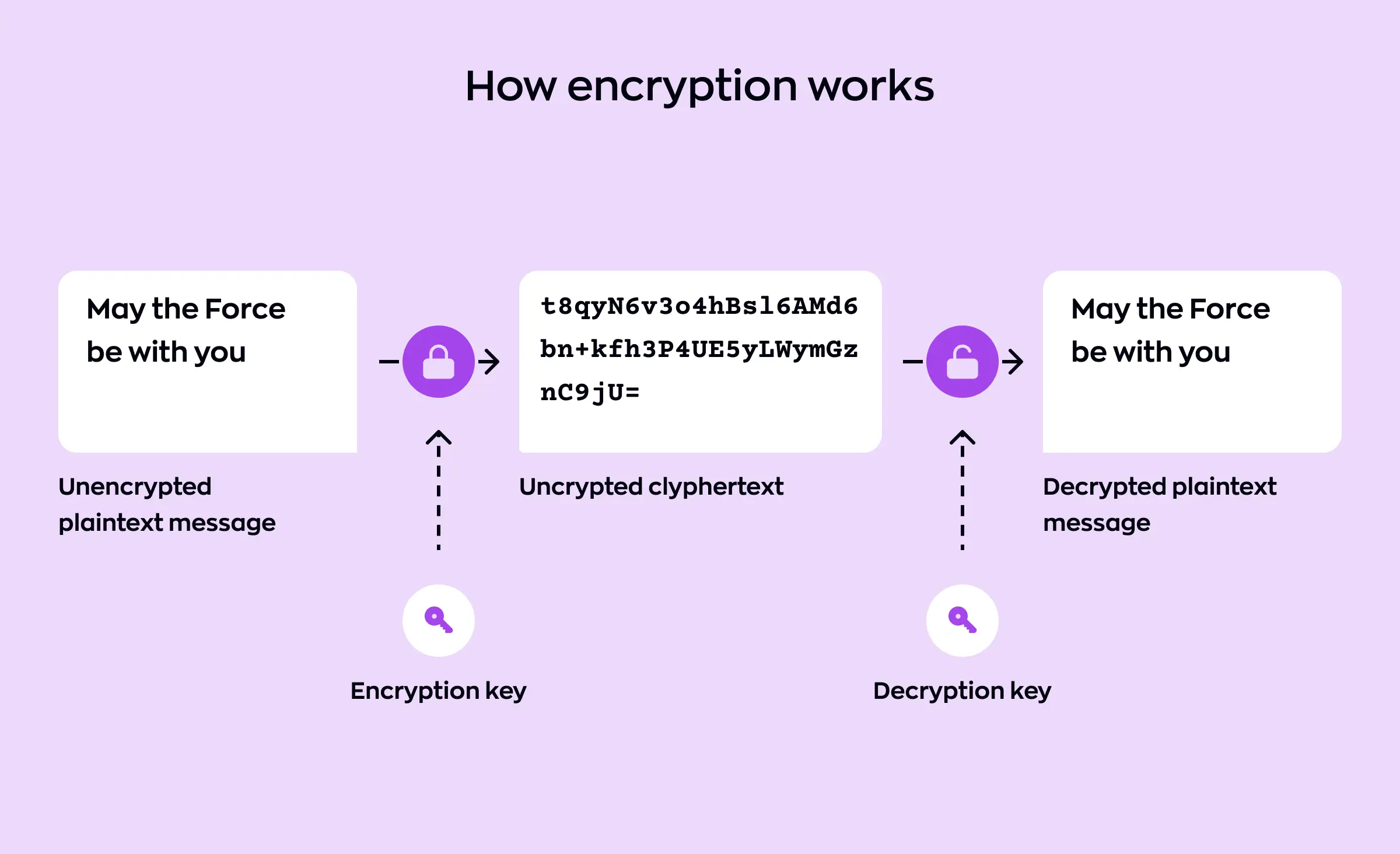
One of the most effective ways to guard sensitive information is through data encryption API techniques. Encryption means converting data into unreadable code for anyone without the right key. This shields data both during transfer and when stored, making it much harder for hackers to misuse what they intercept. For industries like finance and health, data encryption API is often a legal requirement.
Secure coding and design
Solid data protection starts during API development. Developers must follow secure coding practices to prevent leaks and block the most common attacks. This includes checking all code for flaws that hackers exploit, such as those leading to accidental data exposure. Secure API design goes hand in hand with this approach, ensuring that security is built into every system, not pasted on afterward.
Input validation and rate limiting
A leading cause of data protection cyber threats is accepting data at face value. By applying strict input validation API rules, companies force incoming data to meet clear standards and block hidden malware or unsafe commands. Additionally, rate limiting API requests helps prevent attackers from overwhelming your systems or forcefully draining information. Both steps are vital for robust application security.
Data privacy and integrity
Data privacy is top-of-mind for today's businesses. Customers want to know their information is used only for intended purposes, not exposed or resold accidentally. Safeguarding privacy means having strong controls on who can access which data and when. Along with this, companies should monitor data integrity, ensuring that stored information is not altered or corrupted by mistake or through an attack.
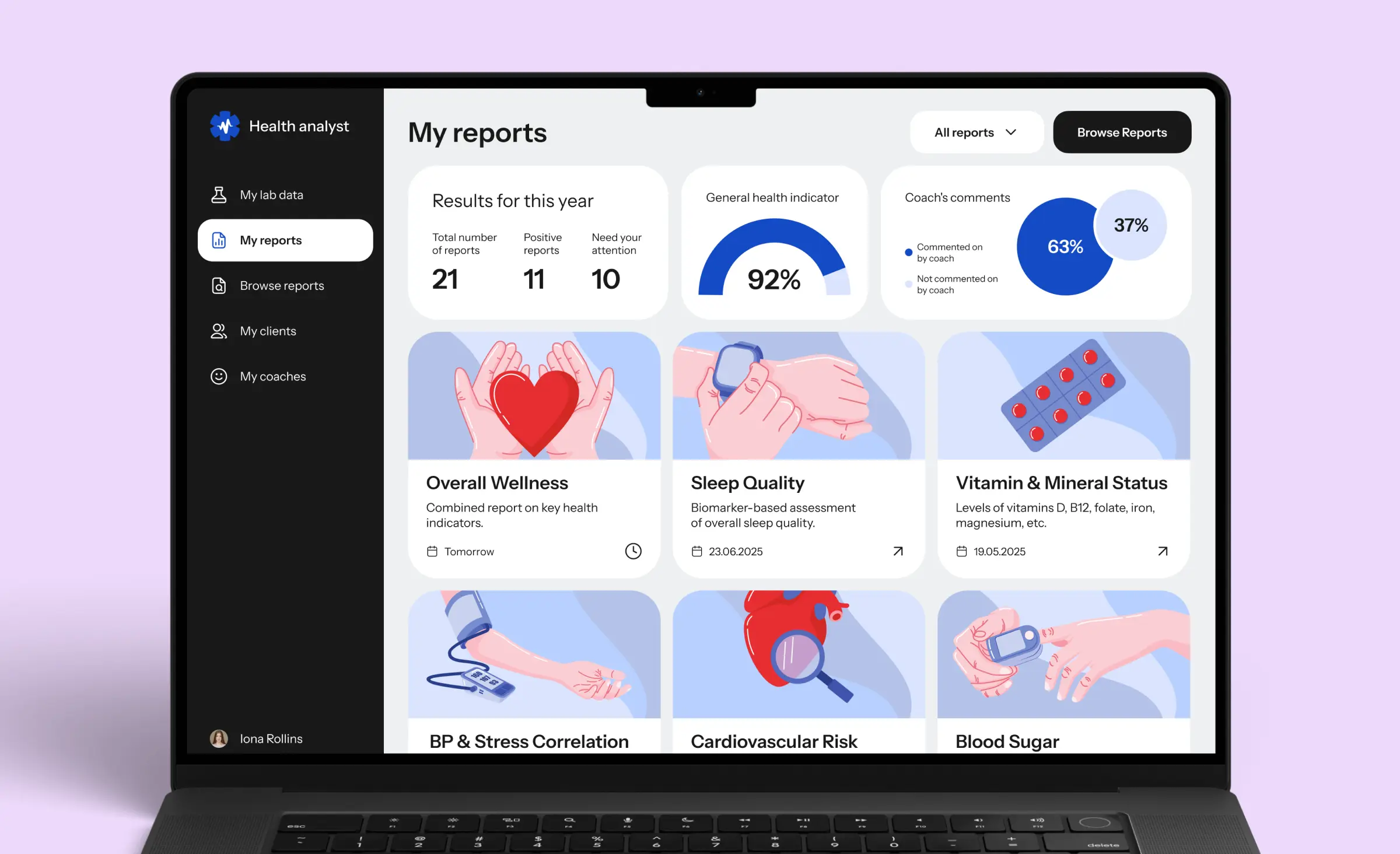
Application security in different industries
More than perhaps any other sectors, fintech security and healthcare security demand flawless execution of application security principles. A lapse in data encryption or input validation can expose accounts, personal health records, or even financial transactions. These industries set an example for others, adopting API security best practices early and investing heavily in preventative measures.
To stay ahead, businesses need to see data protection as an ongoing process, not a one-time fix. Secure coding practices, regular reviews, and updates should be part of the API development lifecycle. This proactive approach strengthens API integrations and supports data privacy, helping companies avoid both emerging risks and costly penalties.
API security across the development lifecycle
API development has become a vital part of building modern products and services. But to stay ahead of threats, security can't be an afterthought. Following secure software development principles from the earliest design steps ensures that flaws are caught before they make it to production. This mindset leads to stronger outcomes across both backend development and customer-facing features.
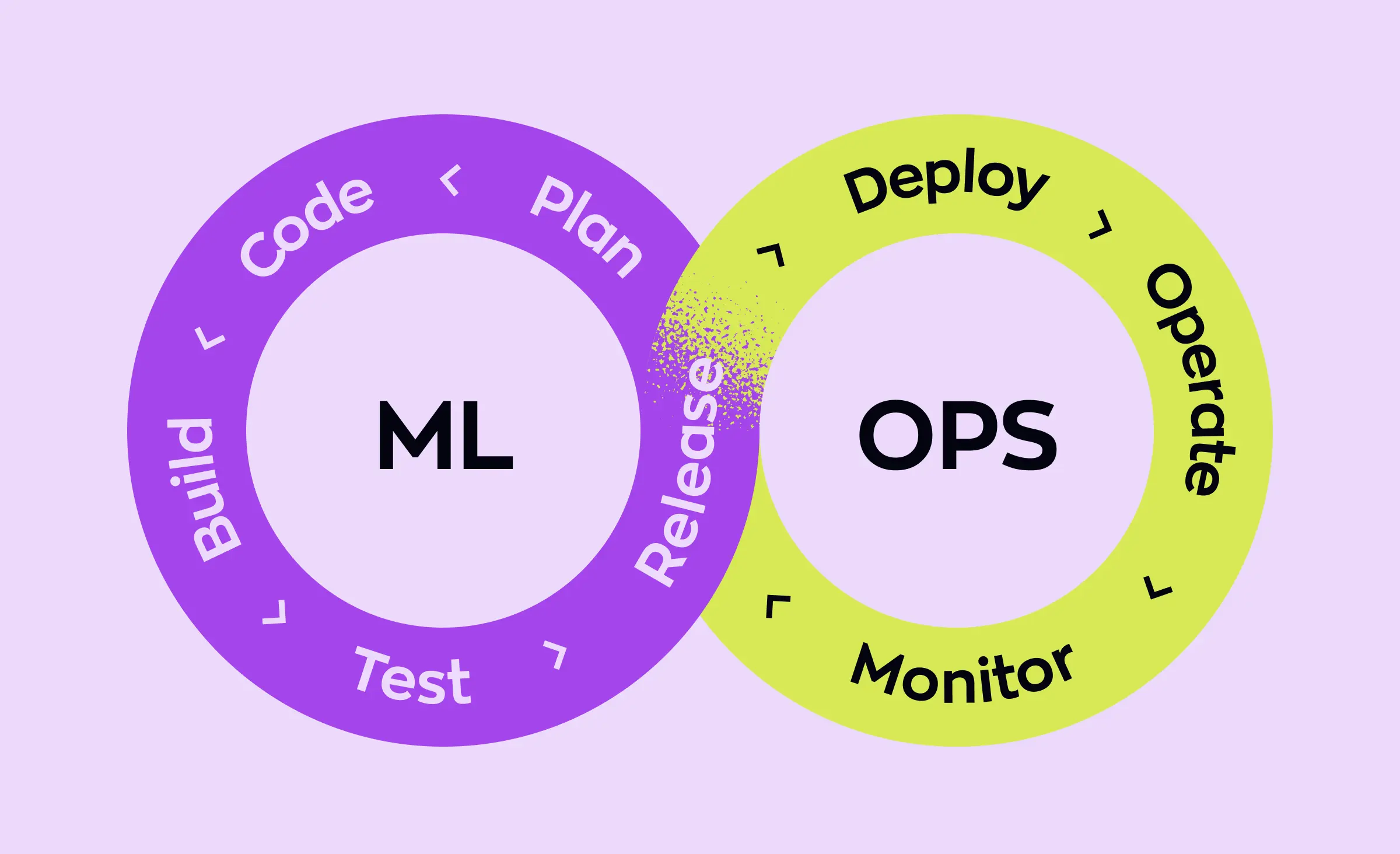
DevOps
Security and speed must go hand in hand. That's why leading companies incorporate DevOps security into their daily routines. Automated security scans and testing run as part of CI/CD pipelines, flagging even the smallest errors before they become major exposures. This approach is especially helpful for organizations with frequent API development cycles and rapid backend development.
Microservices and cloud environments
As systems spread out across multiple services, microservices security and cloud security become non-negotiable. Each microservice may have its own API, which means hundreds or even thousands of endpoints to secure. By using secure integrations and strong access controls, companies reduce the risk that a single weak spot could threaten the entire platform.
With the shift to cloud environments, organizations face new challenges. API gateway security tools help control traffic, monitor access, and stop malicious calls before they reach sensitive resources. In cloud-native systems, setting up proper gateway controls and policies is now a core part of secure software development.
Best practices
Secure coding practices are the backbone of any defensive posture. By teaching development teams to think like attackers — using the OWASP API security top 10 as a guide — common flaws can be identified and fixed early. Strong input validation API strategies and thorough testing limit entry points for malicious data and help defend business operations at every level.
The lifecycle doesn't end at launch. Ongoing API vulnerability management is critical. Regular scans, penetration tests, and real-time monitoring help spot new threats as they emerge. DevOps security workflows make it easier to update or patch APIs on the fly, without gaps in protection or long downtimes.
Holistic visibility for better cybersecurity
A unified approach to API security gives organizations real insight into their systems. With proper dashboards and automated alerts, businesses can see and address issues before attackers can take advantage. This helps in protecting API integrations across various teams and partners, and is especially important when APIs interact with third-party providers or legacy systems.
Robust cybersecurity depends on collaboration. From backend development to DevOps security teams, everyone needs clear ownership over API development and secure integrations. Investing in these practices not only protects companies from risk but also builds trust with users and partners as your platform grows.
How Ronas IT can help with robust API security
Security-first approach
At Ronas IT, we follow API security best practices from day one. Our API development projects always begin with secure software development, using certified technologies and strict DevOps security. We use open-source frameworks like Laravel for backend development, leveraging built-in features to protect against common data protection cyber threats and improve application security.
Protecting API integrations and building for scale
Protecting API integrations is a priority in our backend development. We set up API gateway security for traffic control, authentication, and DDoS protection. We monitor access and defend critical endpoints, meeting requirements for fintech security and healthcare security.
Strong authentication and access controls
For digital identity and authentication, we use trusted platforms such as OAuth2, ensuring that only verified users or partners can access your APIs. Our secure integrations also ensure only authorized users and partners connect to your services.
Cloud security
We deploy cloud security solutions using Google Cloud or AWS, with services like Cloud SQL, Amazon RDS, and Kubernetes for scalability and uptime. All sensitive data benefits from automated encryption in transit and at rest, audit trails, and fine-grained access via IAM. To support secure software development and API vulnerability management, we run automatic tests with SonarQube and GitLab CI, maintaining high code coverage and rapid patching.
Microservices
Our DevOps security team uses Infrastructure as Code approach, Kubernetes for container orchestration, and continuous monitoring tools like Prometheus and Grafana to identify issues before they become problems. Microservices security is built into our architecture, with isolated services, automated failover, and easy updates for compliance. We also help clients with security audits, access controls, and employee training to keep everyone informed about best security practices.
Whether you need backend development for your next application, or want secure API design for enterprise environments, Ronas IT delivers. Our focus is always on protecting API integrations, maintaining secure integrations, supporting business growth, and defending against evolving data protection cyber threats.
Conclusion
API security best practices are now essential for any business undergoing digital transformation. By investing in secure software development and robust application security, you defend your company against a wide range of data protection cyber threats. Protecting API integrations takes more than strong code — it requires end-to-end API authentication authorization and thoughtful cybersecurity for APIs at every stage.
As attackers grow more sophisticated, successful businesses rely on multiple layers of defense. A proactive approach to cybersecurity for APIs not only protects sensitive information today, but also lays the groundwork for future innovation. By prioritizing API authentication authorization and consistent best practices, you keep your users' data safe and your integrations strong.
Partnering with experts helps in protecting API integrations and brings peace of mind, allowing you to focus on growth while your systems stay secure and resilient.



















